Explain Different Security and Integrity Threats to the Database
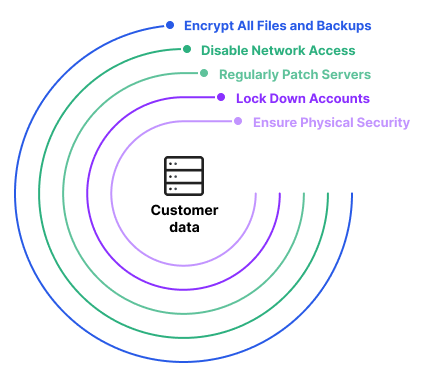
Outsider or external threats are those that come from outside of the organization and usually are carried out by hacktivists other countries and even competition. Database security begins with physical security for the systems that host the database management system DBMS.

Properties Of Database Security Download Scientific Diagram
The most common database threats include.
. Data integrity is enforced using the following three integrity constraints. Moreover human faults storage attrition and several other problems can make it unmanageable for data operators to obtain information from a database. These listed circumstances mostly signify the areas in which the organization should focus on reducing the risk that is the chance of incurring loss or damage to data within a database.
Loss of data privacy. Its a central focus of many data security programs achieved through backup and replication database constraints validation processes all. The challenges of the security program are to ensure that data is maintained in the state that is expected by the users.
Its worth noting that the security solutions can target multiple threats so dont limit yourself to trying one of them if you suspect a single culprit such as a virus. Loss of availability of data. Here are 10 data threats and how to build up your defences around them.
Network Attacks against Integrity. Data integrity is essential for businesses. Corrupted as a result of faulty disks disk drives or power failures.
Loss of confidentiality or secrecy. Because databases are nearly always network-accessible any security threat to any component within or portion of the network infrastructure is also a threat to the database and any attack impacting a users device or workstation can threaten the database. Protecting data against external factors such as natural calamities power outages or hackers falls under the domain of physical integrity.
Importance of Security in Database Environment. THREATS to security and integrity A threat is any situation event or personnel that will adversely effect the database security and smooth and efficient functioning of the organization. The database community basically needs techniques and some organizational solutions to assess and attest the quality of data.
Weve come a long way from Elk Cloner the 1982 Apple virus created by a secondary. Data integrity is most often talked about with regard to data residing in databases and referred to as database integrity as well. If users are granted database privileges that exceed their use or requirements then these privileges can be used to gain some confidential information.
Encryption is one of the most effective types of database security which protect your database from unauthorized access during storing and transmission over the internet. Lets discuss them one by one. Data integrity in the database is the correctness consistency and completeness of data.
Lost or damaged during a system crash - especially one affecting the hard disk. Although the security program cannot improve the accuracy of the data that is put into the system by users. For example deducting a very small.
The threats can be categorized as follows. What is Database Security. Data integrity refers to whether or not there are errors in your data like if its valid and accurate.
Social Engineering is type of attack in which someone with very good interactive skills manipulates others into revealing information about network that can be used to steal data. Key threats to data security. Challenges of database security in DBMS.
Thus database security must extend far beyond the confines of the database alone. Cryptography is excellent for protecting the confidentiality of data at rest and data in motion but keep in mind that it imposes computational complexity and increases latency so it should be used with caution in time-sensitive systems. Data tampering Eavesdropping and data theft.
Data security threats can be divided into insider and outsider threats. Data integrity is preserved only if and when the data is satisfying all the business rules and other. Integrity is the ability to ensure that a system and its data has not suffered unauthorized modification.
Data security is not the same as data integrity. The threats identified over the last couple of years are the same that continue to plague businesses today according to Gerhart. Integrity protection protects not only data.
Entity Integrity - This is related to the concept of primary keys. Threat to a database may be intentional or accidental. When evaluating database security in.
For example in a data breach that compromises integrity a hacker may seize data and modify it before sending it on to the intended recipient. All tables should have their own primary keys which should uniquely identify a row and not be NULL. Integrity is the protection of system data from international or accidental unauthorized changes.
Database security is the business of the entire organization as all people use the data held in the organizations database and any loss or corruption to data would affect the. Credential Threats Employing substandard password management and authentication methods can allow identity theft brute force attacks and social engineering schemes such as phishing. Database security is the protection of the database against intentional and unintentional threats that may be computer -based or non- computer -based.
Backup and recovery procedures. Referential Integrity - This is related to the. Database security includes a variety of measures used to secure database management systems from malicious cyber-attacks and illegitimate use.
Some security controls designed to maintain the integrity of information include. Salami attacks are a series of minor data security attacks that together result in a larger attack. Database Management system is not safe from intrusion corruption or destruction by people who have physical access to the computers.
Common methods include ransomware phishing attacks and hacking. There are different types of encryption algorithm such as AES MD5 and SHA 1 which are used to encrypt and decrypt the all types of sensitive data. Forgotten databases or new ones that the security team does not know about can be a serious database security and integrity threat.
Such as data quality intellectual property rights and database survivability. Database security programs are designed to protect not only the data within the database but also the data management system itself and every application that accesses it from misuse. DATABASE THREATS Since database contains vital information therefore it also faces a lots of threats.
Data Integrity defines a quality of data which guarantees the data is complete and has a whole structure. Top Database Threats. Given below are some database security threats.
Loss of data integrity.
What Is Database Security Threats Best Practices Imperva
Pdf Database Security Threats Prevention
Difference Between Security And Integrity With Comparison Chart
Comments
Post a Comment